Persistent data communication sessions across WAN
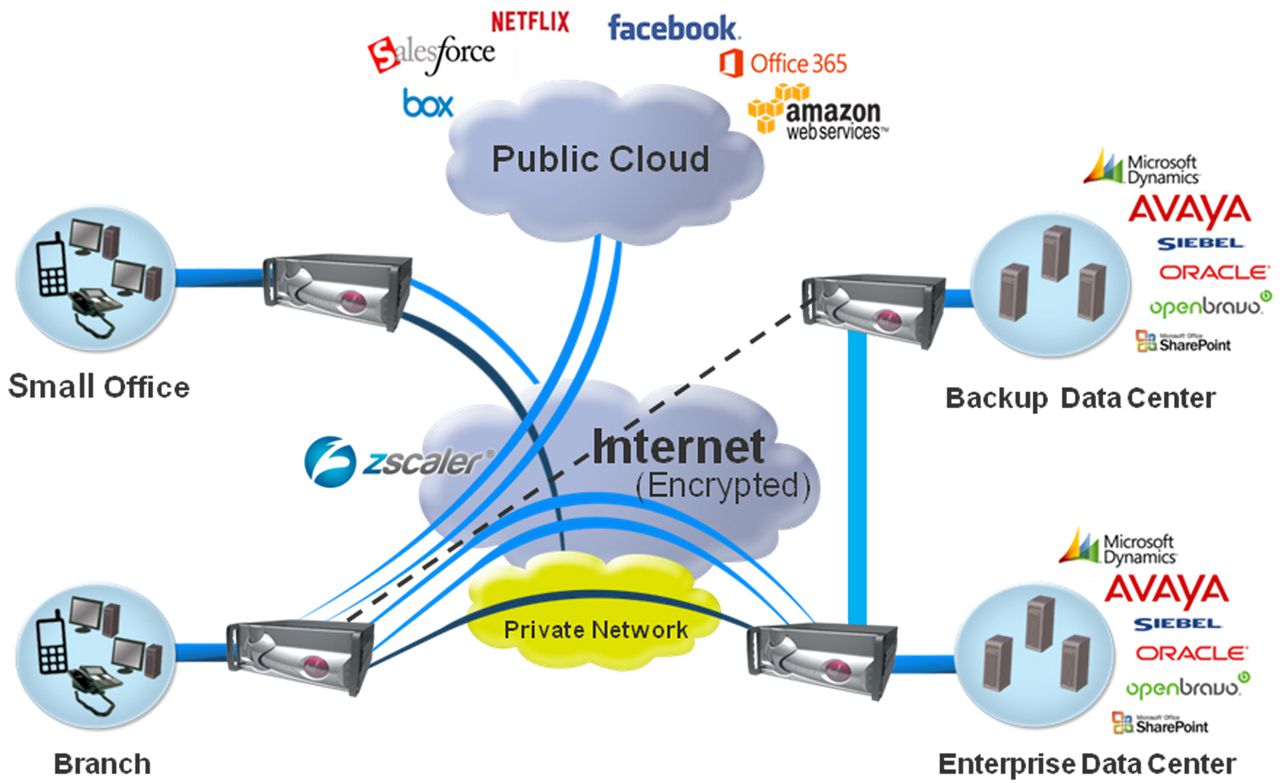
Instead of specifying actual transport layer IP addresses as a basis for a secure tunnel's security association, an approach described herein specifies virtual addresses. Then suitable network appliances intercept and modify packets in order to map between the virtual addresses and actual addresses. The virtual addresses satisfy IPsec or another authentication procedure that checks packets using the security association. The actual addresses are used by transport layer protocols. This overlay approach permits a session to failover from one network connection to another without requiring restoration of the session in a newly created secure tunnel after one of the network interfaces becomes unavailable, thereby obsoleting the security association based in part on the IP address of the now unavailable interface. This innovative approach also allows the use of parallel paths and the use of one-to-many or many-to-one path topologies, which would otherwise not be permitted.