
FatPipe Cybersecurity is an advanced single-stack security solution that can be deployed in both the cloud and on-premise. It fills the gaps of traditional security measures by offering a holistic view of potential threats and seamlessly integrating with cloud platforms. FatPipe Cybersecurity provides network security, cybersecurity, and real-time network and security monitoring, effectively addressing the evolving needs of modern organizations.
Every business, irrespective of their size, is challenged with their own share of vulnerabilities due to their weaker security postures. Security is not a one-size-fits-all strategy; even so, FatPipe takes all the needed measures to provide fortified security to organizations, thus making them less vulnerable to threats.
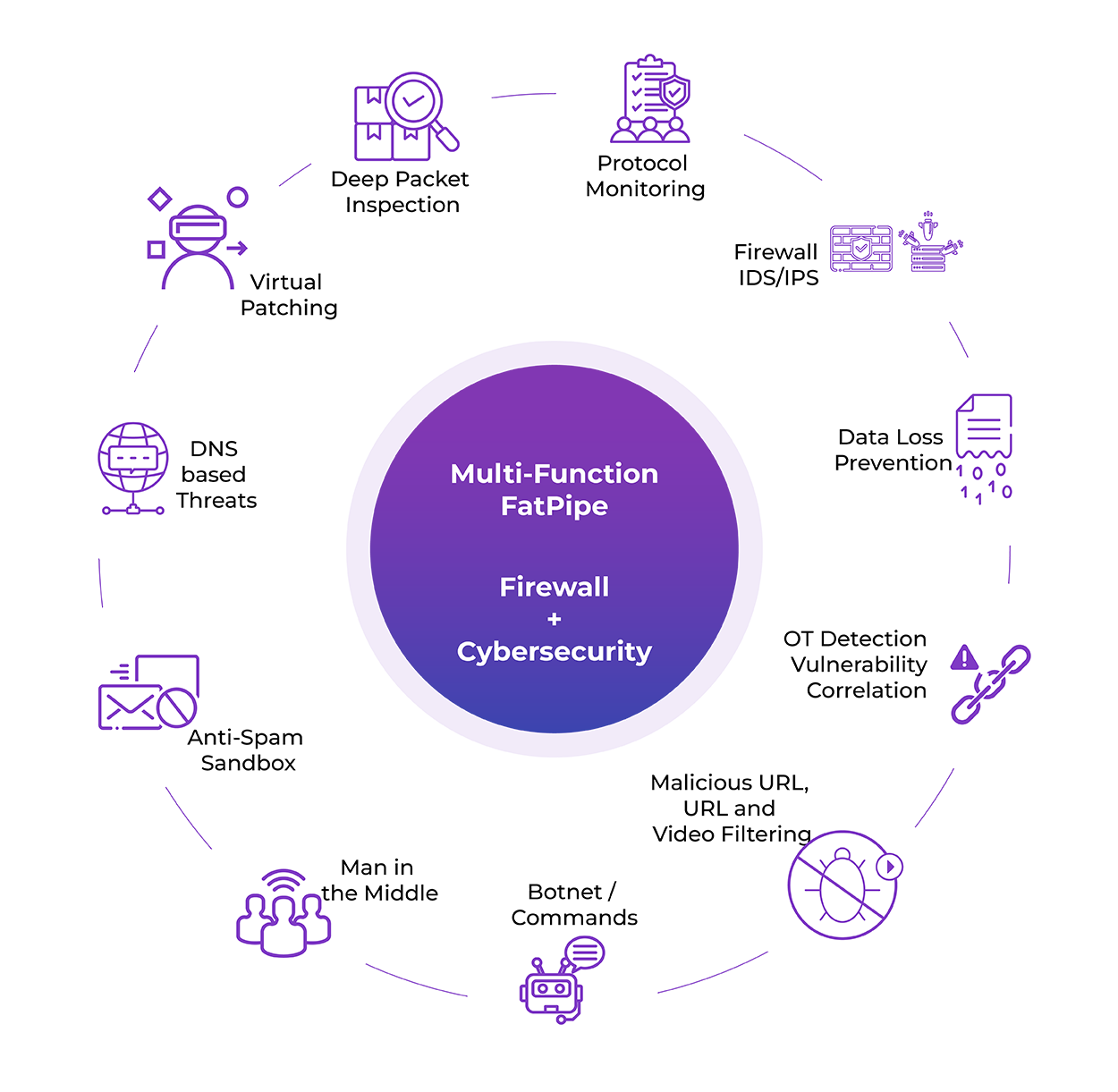
FatPipe delivers a lower total cost of ownership, simplified IT operations, and stronger security outcomes for our customers. Cybersecurity is the result of that approach.
The platform is managed through a single interface with centralized policy control, consistent updates, and no need for separate appliances or management tools. A single administrator can configure and manage the entire system across multiple sites using software-defined policies that simplify deployment and day-to-day management
Cybersecurity uses a proxy-based antivirus engine that inspects downloaded files and email attachments before they reach the end user.
Content is temporarily cached and scanned through a dedicated antivirus process. Once the scan is complete, the clean file is delivered to the user. This process provides accurate threat detection without affecting network stability or performance.
Yes. Cybersecurity is the foundation of FatPipe’s unified SASE framework, combining WAN edge control with in-line, cloud-delivered security.
It provides secure access for remote and distributed users through policy-driven routing, resilient multipath data paths, quality-of-service enforcement, and integrated Zero Trust principles. The platform delivers Secure Edge capabilities that control access at the network perimeter while maintaining reliable connectivity for cloud applications.